In today’s rapidly evolving technological landscape, virtually all software ecosystems are susceptible to a myriad of security threats. These threats are escalating in sophistication and scale, evidenced by a 151% surge in malware exploiting software vulnerabilities in Q2 2018 alone. Furthermore, it’s projected that by 2021, the financial repercussions of cyber-crime will skyrocket to an annual toll of $6 trillion. These threats, emanating from both external and internal sources, can wreak havoc—crippling systems or compromising sensitive data, thereby eroding consumer confidence in the affected organizations.
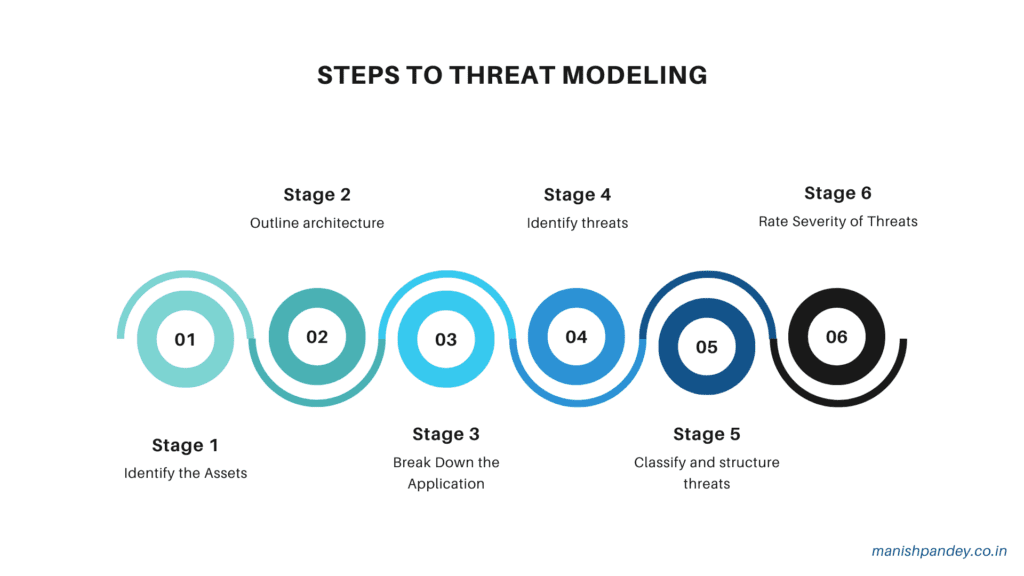
To mitigate these risks, system administrators leverage various threat-modeling methodologies. These methodologies serve as a strategic framework to fortify defenses, encompassing:
- System abstractions to outline the structure and components.
- Profiles detailing potential attackers, their objectives, and methodologies.
- Catalogs enumerating potential threats.
The landscape of threat modeling is diverse, with numerous methodologies developed over the years. These can be synergized to provide a comprehensive, multi-faceted perspective of potential vulnerabilities. However, it’s crucial to note that these methodologies vary—some focus on abstract system aspects, while others are more people-centric, emphasizing risk and privacy concerns.
The essence of threat modeling lies in its ability to aid threat intelligence analysts in the identification, classification, and prioritization of threats. This is pivotal for crafting effective documentation and enhancing the operational capabilities of security teams in safeguarding IT assets.
Ideally, threat modeling should be integrated early in the development lifecycle to detect and rectify potential security issues promptly, thereby circumventing more costly interventions later. It also informs proactive architectural decisions that inherently minimize security risks from the outset, particularly relevant in the realm of cyber-physical systems—like smart cars, cities, and grids—which blend software with physical infrastructure and are exposed to unique vulnerabilities.
This blog has delineated 13 distinct threat-modeling methodologies derived from various authoritative sources, each tailored to different aspects of the threat assessment process. While no single methodology is universally preferable, the choice should align with the specific security needs of the project at hand. Please note these are not the only methods out there other methods like checklist based approach or OWASP top 10 or OWASP ASVS or MITRE ATT&CK based approaches are also utilized.
As you consider adopting a threat modeling approach, it is imperative to understand the nuances in methodology, process, and objectives. Among the plethora of methodologies available, here are six prevalent ones that are instrumental in assessing and prioritizing threats to IT infrastructures. Each methodology must be evaluated to ensure it aligns with the organization’s specific business goals and delivers actionable threat intelligence.
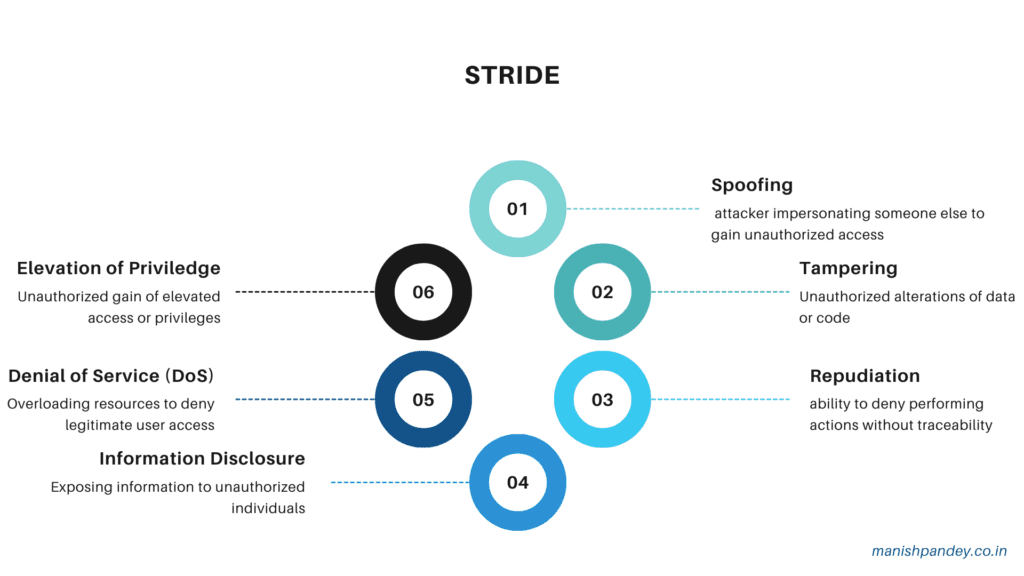
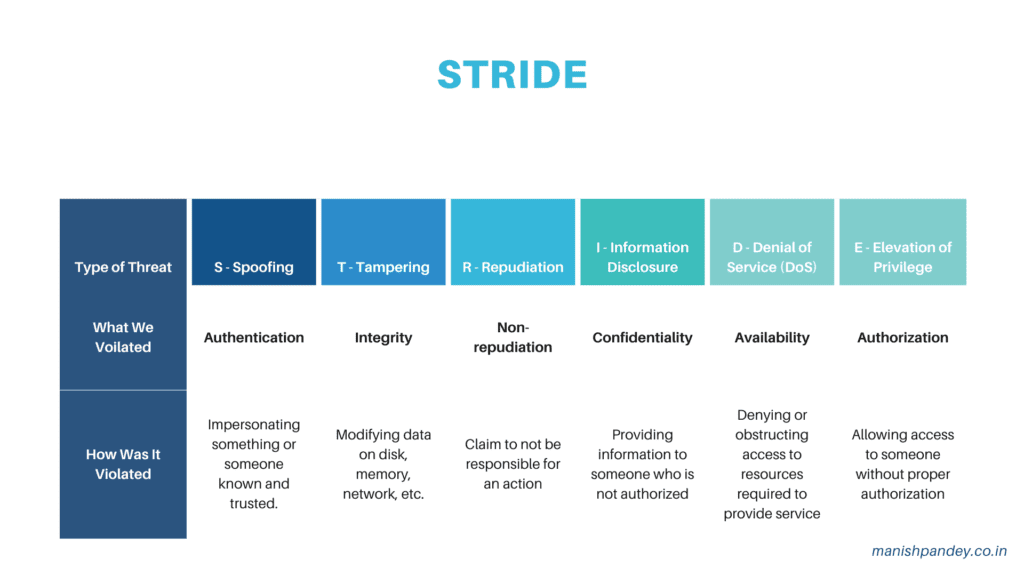
STRIDE: A Cornerstone in Threat Modeling Landscape
Originating in 1999 and embraced by Microsoft by 2002, STRIDE stands as the pinnacle of threat modeling methodologies, recognized for its comprehensive maturity. Over the years, STRIDE has continuously evolved, integrating nuanced threat-specific tables along with its derivatives—STRIDE-per-Element and STRIDE-per-Interaction.
STRIDE systematically dissects the intricacies of system design, focusing on the operational framework. Utilizing data-flow diagrams (DFDs), it meticulously maps out system entities, events, and demarcations. This methodology employs a universally recognized set of threats, encapsulated by its mnemonic acronym, to enhance system resilience against potential security breaches.
Though no longer directly maintained by Microsoft, STRIDE is an integral component of the Microsoft Security Development Lifecycle (SDL). It is supported by the Microsoft Threat Modeling Tool, ensuring its ongoing relevance and applicability. In addition, Microsoft has developed the DREAD methodology, another mnemonic-based approach that offers a distinct perspective for evaluating threats, emphasizing aspects like damage potential, reproducibility, exploitability, affected users, and discoverability.
STRIDE’s robust framework has proven effective across both purely digital and cyber-physical systems, underscoring its versatility and enduring significance in the realm of cybersecurity threat assessment.
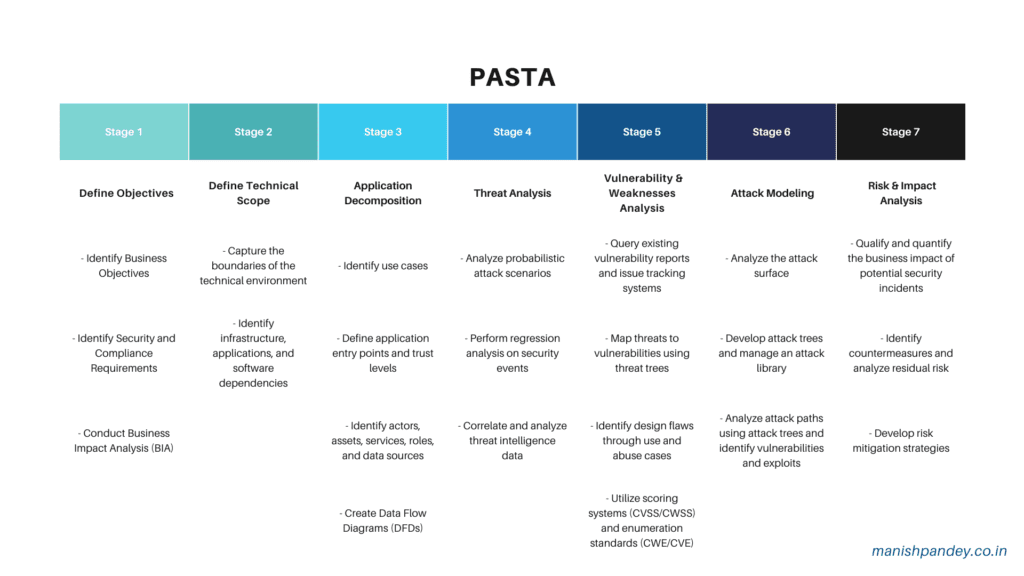
PASTA: A Holistic Approach to Risk-Centric Threat Modeling
Introduced in 2012, the Process for Attack Simulation and Threat Analysis (PASTA) is a comprehensive, risk-centric threat-modeling framework. It encapsulates a structured seven-step methodology, each step encompassing multiple activities, aimed at simulating attacks and analyzing potential threats. This framework is depicted in available literature and visual representations like Figure 1, adapted from “Threat Modeling w/PASTA: Risk-Centric Threat Modeling Case Studies.”
PASTA strategically bridges business imperatives with technical specifications, utilizing an array of design and elicitation tools across its stages. This methodology not only involves but requires the active participation of key stakeholders—spanning operations, governance, architectural design, and development. Its design ensures that threat modeling transcends operational tactics to become a strategic component of organizational security infrastructure.
Renowned for its attacker-centric approach, PASTA delivers an asset-centric output. This is achieved through meticulous threat enumeration and scoring, providing a granular and actionable security posture. Each stage of the PASTA framework is designed to progressively identify, enumerate, and prioritize threats, enabling organizations to tailor specific, effective countermeasures. This systematic approach ensures a comprehensive understanding and mitigation of risks, aligning with both organizational security goals and business objectives.
LINDDUN: Enhancing Privacy Through Systematic Assessment
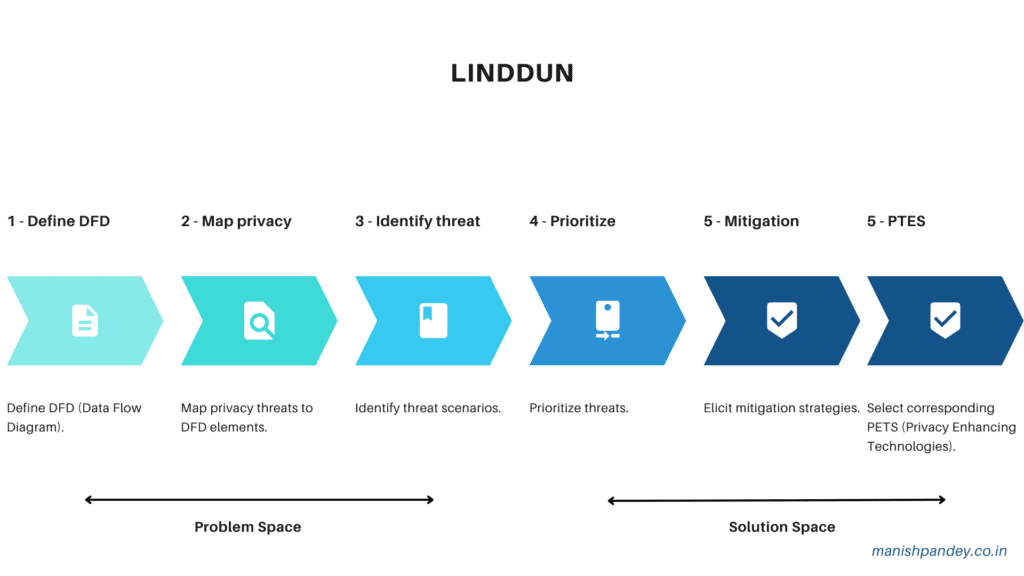
LINDDUN, an acronym that stands for Linkability, Identifiability, Nonrepudiation, Detectability, Disclosure of Information, Unawareness, and Noncompliance, is a framework meticulously designed to address and mitigate privacy concerns within data security realms. This methodology is laid out in a structured six-step process, illustrated in available references such as Figure 2 from “Threat Modeling: 12 Available Methods.”
The LINDDUN framework initiates with the development of a Data Flow Diagram (DFD) that meticulously outlines the system’s data flows, data stores, processes, and external entities. This foundational step is critical as it sets the stage for a comprehensive evaluation of the system’s privacy posture.
Through a methodical review of each element within the model, LINDDUN users engage in an in-depth analysis from the perspective of predefined threat categories. This rigorous analysis facilitates the identification of relevant threats and the subsequent construction of threat trees. These trees effectively map out potential privacy vulnerabilities, providing a clear pathway for addressing and mitigating privacy risks.
LINDDUN’s systematic approach not only ensures a thorough privacy assessment but also aligns with strategic organizational objectives to safeguard sensitive data against a spectrum of vulnerabilities. This makes LINDDUN an essential component of any robust privacy and data security strategy.
CVSS: Standardizing Vulnerability Assessment
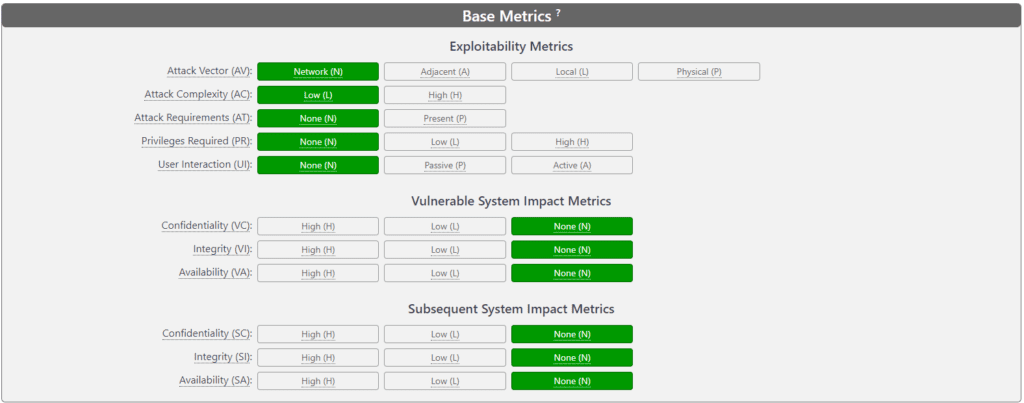
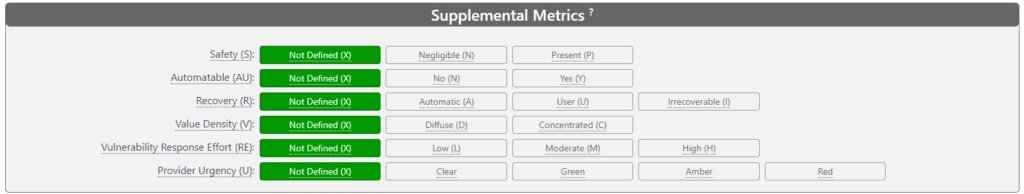
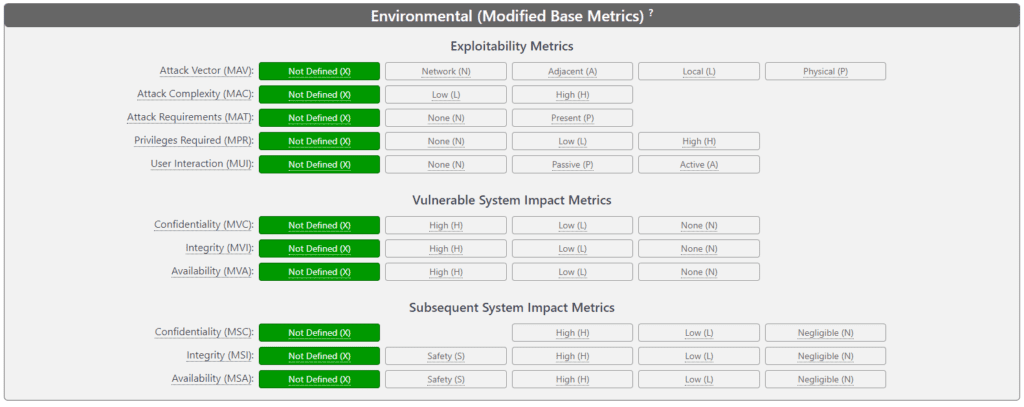
The Common Vulnerability Scoring System (CVSS) represents a pivotal framework developed under the auspices of the National Institute of Standards and Technology (NIST) and is presently maintained by the Forum of Incident Response and Security Teams (FIRST), with ongoing enhancements contributed by the CVSS Special Interest Group. This system plays a critical role in encapsulating the essential attributes of security vulnerabilities and translating these into a quantifiable severity score, thereby standardizing vulnerability assessments across diverse cyber and cyber-physical environments.
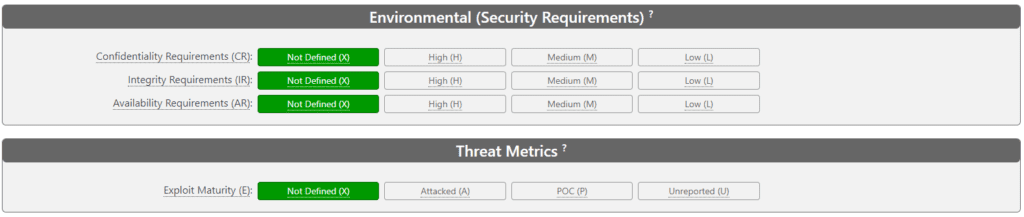
CVSS is structured around three core metric groups: Base, Temporal, and Environmental, each comprising a specific set of metrics as depicted in various illustrative resources such as Figure 3 from the “Threat Modeling: 12 Available Methods” document.
The determination of a CVSS score involves assigning specific values to these metrics based on thorough analysis by a security analyst. This process is supported by detailed documentation that guides the scoring, ensuring a uniform approach to threat assessment. Additionally, the CVSS framework is often utilized in conjunction with other threat-modeling methodologies, enhancing its applicability and effectiveness in comprehensive security evaluations.
A key feature of the CVSS is its accessibility through an online calculator, enabling users to dynamically compute vulnerability scores and thereby facilitate prompt and informed security decision-making. This integration of CVSS scores into broader security management practices underscores its significance as a fundamental tool in the arsenal of cybersecurity professionals.
CVSS 4.0 Calculator
Attack Trees: A Foundational Method for Systematic Threat Modeling
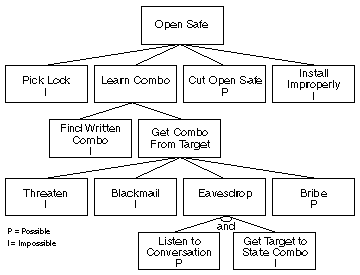
Attack trees represent a foundational and extensively utilized methodology for modeling threats across diverse domains, including cyber-only systems, cyber-physical systems, and purely physical systems. Originally deployed as an autonomous approach, attack trees have increasingly been integrated with other methodologies and frameworks to enhance their comprehensive applicability.
Structured as hierarchical diagrams, attack trees visually map out potential attacks on a system. The apex of the tree symbolizes the ultimate objective of the attack, while the branches—or leaves—enumerate various tactics to achieve this goal. Each distinct attack objective is articulated through a separate tree, collectively forming a robust set of attack trees that facilitate a thorough system threat analysis, as illustrated in Figure 4 from the document “Threat Modeling: 12 Available Methods.”
In scenarios involving intricate systems, attack trees can be meticulously crafted for individual components rather than the system as a whole. This granularity enables administrators to utilize these trees strategically to inform security protocols, assess system vulnerabilities, and evaluate specific attack vectors.
In recent years, the integration of attack trees with other strategic methodologies like STRIDE, CVSS, and PASTA has become commonplace, underscoring their value in a holistic security strategy framework. This synergy enhances the ability to pinpoint and mitigate potential threats effectively, reinforcing the relevance of attack trees in contemporary cybersecurity landscapes.
Persona non Grata (PnG): A Human-Centric Approach to Threat Modeling
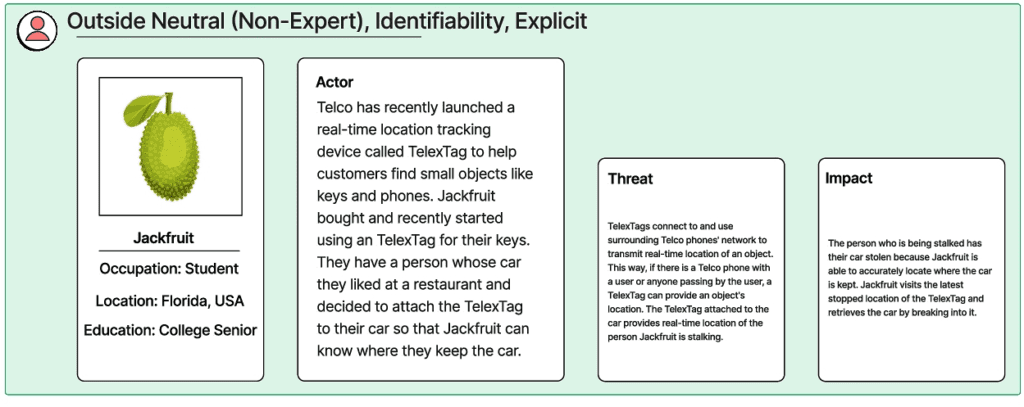
Persona non Grata (PnG) is a specialized threat modeling methodology that emphasizes the motivations and capabilities of human attackers. It categorizes potential users into archetypes capable of misusing a system, compelling analysts to adopt a perspective centered on unintended use. This method is particularly effective in visualizing threats by representing the adversary’s viewpoint, as can be seen in various examples illustrated in Figure 5 from “Threat Modeling: 12 Available Methods.”
PnG is instrumental during the initial phases of threat modeling. It facilitates a deep dive into the psychological and technical profile of potential attackers by introducing security analysts to the conceptual persona of an adversary. This exercise entails a detailed examination of the attacker’s skills, motivations, and objectives, enabling analysts to identify and understand system vulnerabilities explicitly from the attacker’s perspective.
Moreover, PnG seamlessly integrates into Agile methodologies, which often employ personas to simulate user interaction with systems. This compatibility enhances its applicability in dynamic development environments, allowing for iterative and persona-driven assessments that align with Agile cycles. Consequently, PnG not only aids in fortifying systems against human-centric threats but also complements contemporary Agile practices, making it a versatile tool in strategic security planning and implementation.
Security Cards: Enhancing Threat Identification through Collaborative Brainstorming
Security Cards are an innovative and collaborative brainstorming tool designed to uncover unusual and complex security threats. While not a formalized method, these cards serve as a dynamic facilitation mechanism in security analysis and planning sessions. By employing a deck of cards, which can be seen in examples like Figure 6 from the document “Threat Modeling: 12 Available Methods,” analysts are prompted to explore a range of critical questions related to potential security incidents:
- Who might launch an attack?
- Why might the system be targeted?
- What assets could be of interest?
- How might these attacks be executed?
The use of Security Cards involves a set of 42 distinct cards categorized into four main dimensions that guide the threat discovery process: Human Impact (9 cards), Adversary’s Motivations (13 cards), Adversary Resources (11 cards), and Adversary’s Methods (9 cards). Each category is designed to prompt deep thinking about different aspects of potential security threats, helping teams to systematically identify and assess risks.
This method is particularly useful in settings that benefit from structured yet creative thinking. It encourages teams to engage in depth with potential security scenarios, fostering a comprehensive understanding of threat landscapes and enhancing the overall security posture of organizations.
Hybrid Threat Modeling Method (hTMM): A Comprehensive and Cost-Effective Approach
Developed by the Software Engineering Institute (SEI) in 2018, the Hybrid Threat Modeling Method (hTMM) represents a cutting-edge integration of multiple established methodologies, specifically the Security Quality Requirements Engineering Method (SQUARE), Security Cards, and Persona non Grata (PnG) activities. This method is distinguished by its robust design objectives, which aim to ensure the absence of false positives, comprehensive threat coverage, consistent results irrespective of the practitioner, and overall cost-effectiveness.
The hTMM involves a structured process with key steps designed to maximize the efficacy and efficiency of threat modeling:
- System Identification: Initiate by clearly defining the system that will undergo threat modeling.
- Application of Security Cards: Utilize Security Cards to generate initial threat scenarios based on insights and suggestions from the development team.
- Refinement through PnG: Refine the analysis by discarding Persona non Grata scenarios that do not present realistic attack vectors.
- Results Summarization: Leverage tool support to synthesize and document the findings from the Security Cards and PnG analysis.
- Risk Assessment Integration: Conclude the process by transitioning to a formal risk assessment methodology to further validate and prioritize the identified threats.
By synergizing these diverse methods, hTMM provides a comprehensive framework that not only identifies potential threats but also ensures that these threats are relevant and systematically analyzed. This methodology is especially valuable in environments requiring rigorous and repeatable security analysis without the overhead of extensive resource allocation, making it a preferred choice among organizations striving for high-security standards with cost-effective solutions.
Quantitative Threat Modeling Method: A Precision-Driven Approach for Complex Systems
The Quantitative Threat Modeling Method (Quantitative TMM) represents a sophisticated hybrid approach that integrates the strengths of attack trees, STRIDE, and the Common Vulnerability Scoring System (CVSS) to address and mitigate threats in cyber-physical systems characterized by intricate interdependencies among components.
This method is meticulously structured to enhance the precision and effectiveness of threat modeling in complex environments:
- Component Attack Trees Construction: The initial step involves developing detailed attack trees for each of the five threat categories defined by STRIDE (Spoofing, Tampering, Repudiation, Information Disclosure, Denial of Service, and Elevation of Privilege). This phase is crucial as it lays the foundational framework for illustrating the interconnections between various attack vectors and the underlying component attributes.
- Application of CVSS: Following the establishment of component attack trees, the CVSS framework is employed to quantitatively assess and score the vulnerabilities identified within the components. This scoring is integral as it quantifies the severity of each threat, providing a clear metric to gauge potential impacts and prioritize mitigation efforts.
The Quantitative TMM is designed to provide a comprehensive and quantifiable analysis of threats, thereby enabling more informed decision-making and strategic planning in the protection of cyber-physical systems. By leveraging this method, organizations can achieve a more robust understanding of their security posture and implement targeted defenses against sophisticated threats.
Trike: Comprehensive Security Audit Framework
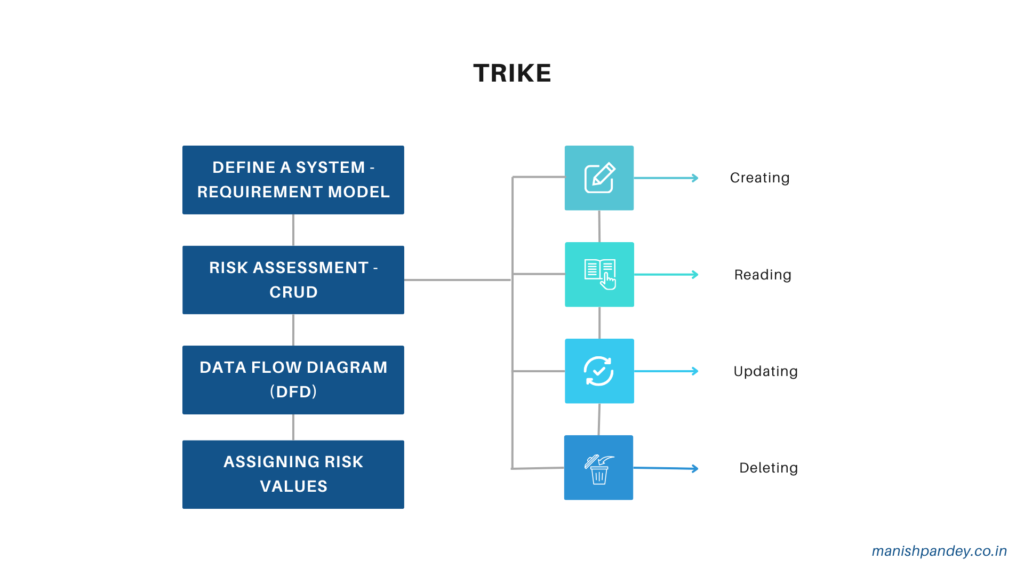
Trike is an innovative security audit framework that employs threat modeling from a dual perspective of risk management and defense. As an open-source methodology, Trike integrates the principles of risk management into the core of its threat modeling process, distinguishing itself through a unique blend of two primary models: the Requirement Model and the Implementation Model.
Requirement Model: This foundational model delineates the security characteristics of an IT system and assigns acceptable risk levels to each asset. It serves as a strategic framework that facilitates coordination across various security teams and stakeholders, ensuring a unified approach to security.
Implementation Model: Following the Requirement Model, the Implementation Model involves the creation of a Data Flow Diagram (DFD) that vividly maps out the flow of data and user actions within the system. This model is critical for the detailed analysis of threats, where each identified threat is enumerated and assigned a specific risk value. Subsequently, appropriate security controls and preventive measures are defined and prioritized based on these risk assessments.
The Trike methodology begins with a precise definition of the system under review. An analyst constructs a Requirement Model by cataloging the system’s actors, assets, intended actions, and governing rules. This step culminates in the development of an actor-asset-action matrix, where assets are listed as columns and actors as rows. Each matrix cell is further divided into four quadrants corresponding to the CRUD (Create, Read, Update, Delete) actions, with each action classified as allowed, disallowed, or rule-bound. Attached to each quadrant is a rule tree that provides detailed governance for actions.
Subsequent to the requirement definition, a DFD is constructed, mapping each element to relevant actors and assets. Through iterative analysis of the DFD, the analyst pinpoints potential threats, categorizing them primarily into elevations of privilege or denials of service, each becoming a root node in an associated attack tree.
Risk assessment within Trike is meticulously quantified using a five-point scale to evaluate the likelihood of attacks impacting assets through CRUD actions. Additionally, actors are assessed on a five-point risk scale (where a lower number indicates higher risk) and a three-dimensional scale (always, sometimes, never) to gauge the consistency of their actions on each asset.
Trike’s structured and quantitative approach not only facilitates a thorough understanding of systemic vulnerabilities but also enhances the strategic implementation of tailored security measures, thereby elevating the overall security posture of the organization.
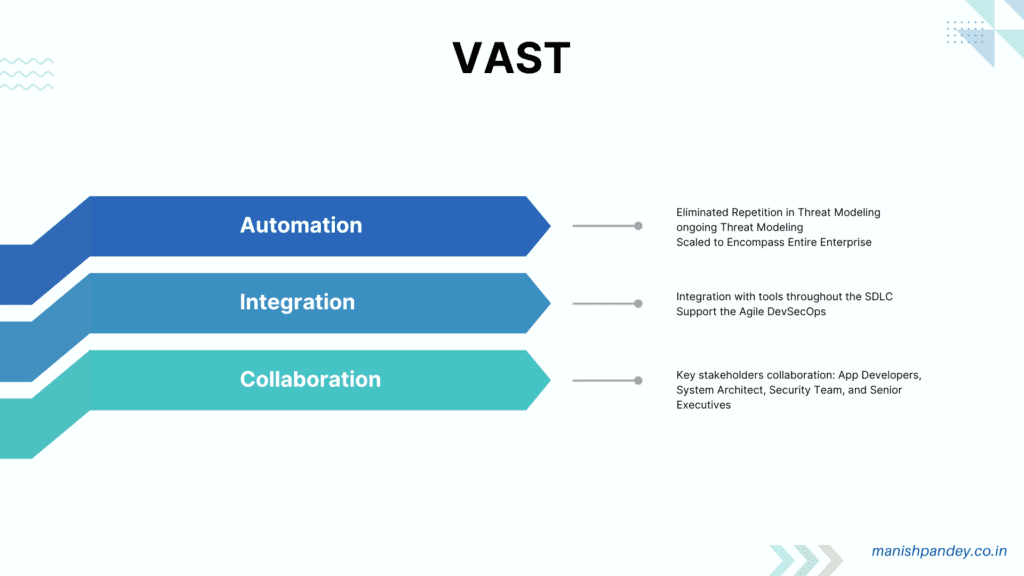
VAST Modeling: Elevating Threat Intelligence Across the Enterprise
The Visual, Agile, and Simple Threat (VAST) Modeling method represents a paradigm shift in how organizations approach threat modeling. Anchored in the capabilities of ThreatModeler—an automated platform—VAST enhances the scalability and usability of threat modeling, making it an integral part of security strategies in large-scale enterprises. This method produces actionable and reliable outcomes that are pertinent across various organizational tiers, ensuring alignment with the strategic goals of diverse stakeholders, including developers, architects, security professionals, and executive leadership.
VAST is distinguished by its comprehensive coverage of the software development lifecycle, seamlessly integrating with existing tools and fostering collaboration across all key organizational players. The methodology’s adaptability makes it a cornerstone in the continuous evolution of security practices within fast-paced development and DevOps environments.
Crucially, VAST differentiates between two primary modeling streams to cater to the distinct needs within the organization:
- Application Threat Models: These models are developed using process-flow diagrams that articulate the architectural nuances of applications. This perspective focuses on how applications are designed and interact within their ecosystem, offering a structured view that is crucial for identifying architectural vulnerabilities.
- Operational Threat Models: Constructed from the attacker’s viewpoint using Data Flow Diagrams (DFDs), these models provide insights into potential operational vulnerabilities. This attacker-centric approach is vital for understanding the practical security challenges that could be exploited during the operational phase of the lifecycle.
By integrating these dual perspectives, VAST ensures a holistic approach to threat modeling. It aligns technical security assessments with organizational processes and bridges the gap between software development and operational security, thereby embedding robust security practices into the fabric of the organization’s development and operational workflows.
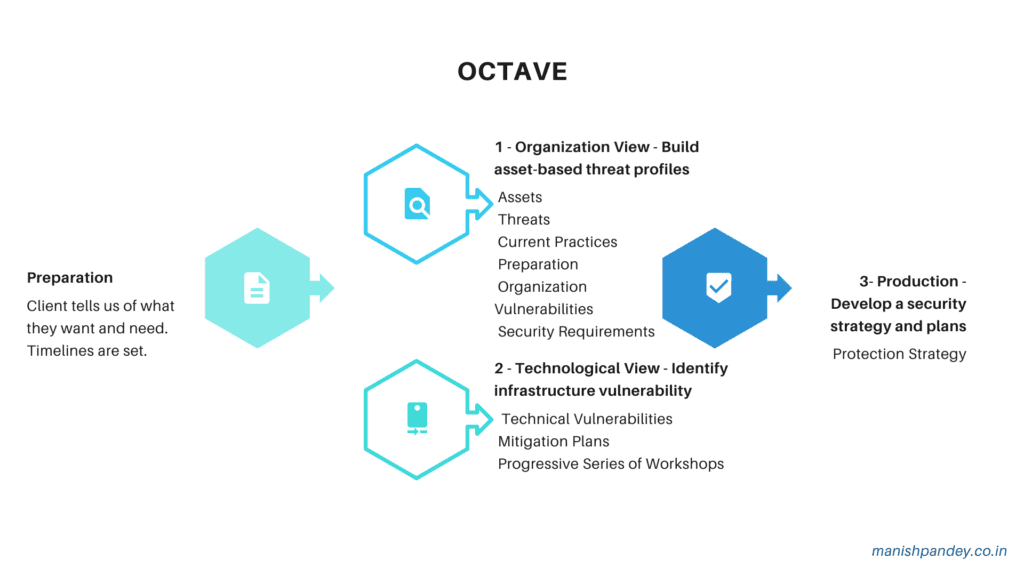
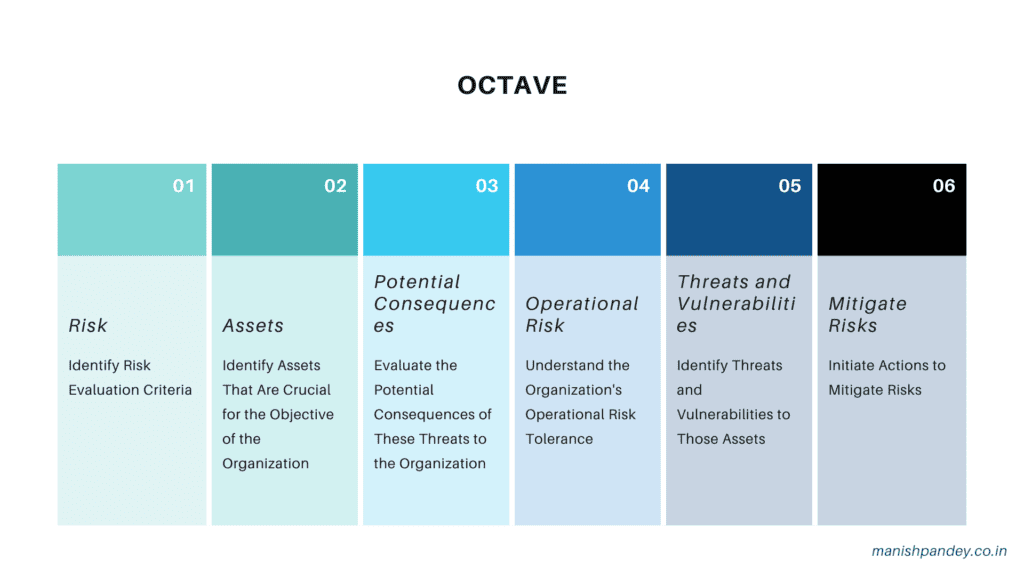
OCTAVE: A Strategic Framework for Operationally Critical Risk Assessment
The Operationally Critical Threat, Asset, and Vulnerability Evaluation (OCTAVE) method, developed by the CERT Division of the Software Engineering Institute (SEI) in 2003 and refined in 2005, is a robust risk-based strategic assessment tool specifically designed for cybersecurity. Unlike methods that focus on technological risks, OCTAVE emphasizes a comprehensive evaluation of organizational risks, integrating operational risk management, security practices, and technology oversight.
OCTAVE’s approach is geared towards identifying, assessing, and managing risks associated with IT assets, focusing on the critical components that underpin information security. This methodology enables organizations to pinpoint the threats that could compromise the confidentiality, integrity, and availability of these assets, thereby facilitating a deep understanding of vulnerable information and devising strategies to mitigate these risks effectively.
Structured in three distinct phases, OCTAVE provides a systematic process for strengthening organizational cybersecurity:
- Build Asset-Based Threat Profiles: This initial phase involves an organizational evaluation to establish profiles that link critical assets to potential threats, providing a clear view of prioritized risk areas.
- Identify Infrastructure Vulnerability: The second phase evaluates the vulnerabilities within the organization’s information infrastructure, aiming to uncover weaknesses that could be exploited by identified threats.
- Develop Security Strategy and Plans: The final phase focuses on strategic decision-making to address identified risks. It involves crafting tailored security strategies and detailed plans to safeguard the organization’s critical assets against potential threats.
OCTAVE’s methodical approach not only underscores the importance of a strategic perspective on cybersecurity but also ensures that risk management is aligned with the organization’s broader operational objectives. This alignment is critical for creating resilient security postures that can adapt to and mitigate evolving threats in a dynamic risk landscape.
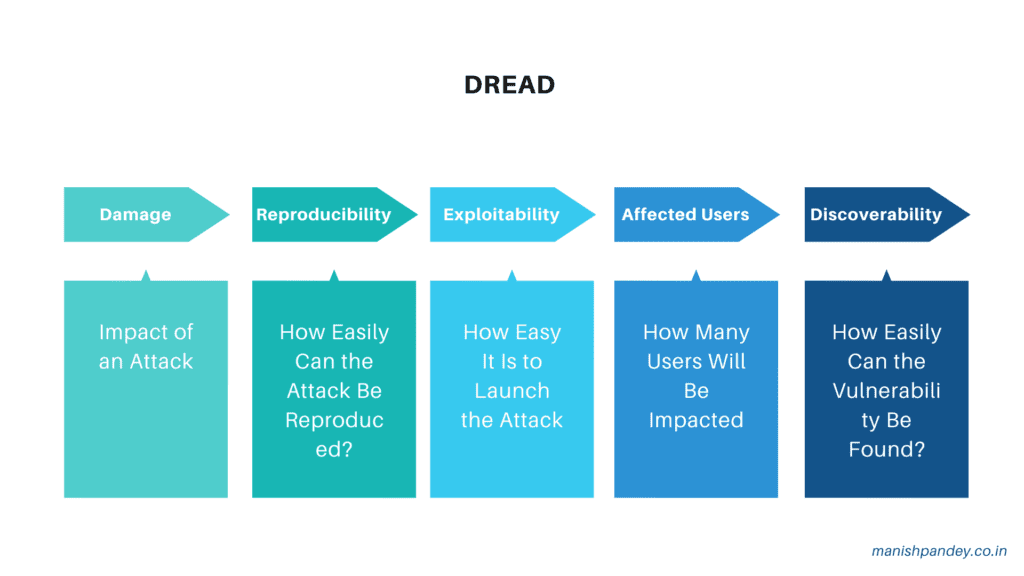
DREAD: A Risk Assessment Framework for Prioritizing Threats
The DREAD methodology is a comprehensive risk assessment tool used to evaluate, analyze, and determine the likelihood of risks associated with cybersecurity threats. Originating from a structured approach, DREAD categorizes and rates potential security threats, facilitating a prioritized and strategic response to mitigate identified risks.
DREAD stands for:
- Damage Potential: Assesses the possible impact of a threat if it were to materialize.
- Reproducibility: Measures how easily a threat can be replicated.
- Exploitability: Evaluates the ease with which an attack can be executed.
- Affected Users: Estimates the number of users or systems that would be impacted by the threat.
- Discoverability: Gauges the likelihood that the vulnerability will be discovered.
By systematically rating threats across these five dimensions, the DREAD methodology enables organizations to quantify and prioritize risks based on their potential severity and the feasibility of their occurrence. This prioritization helps security teams allocate resources effectively and implement targeted security measures to address the most critical vulnerabilities first. The structured assessment provided by DREAD is instrumental in crafting robust security strategies that enhance an organization’s defensive posture against complex cybersecurity challenges.
Wrapping Up and Looking Ahead: Enhancing Security Through Effective Threat Modeling
Threat modeling is an essential process that significantly enhances the security and trustworthiness of your products. Throughout this post, we’ve explored 13 diverse threat-modeling methods, each with its unique attributes and applications. These methods range from standalone applications to integrative approaches that combine multiple frameworks, offering a flexible toolkit for addressing various security, risk, and privacy concerns.
This forthcoming discussion will focus on providing tailored guidance for selecting and utilizing the appropriate threat modeling methods based on specific project needs and contexts.
Selecting the optimal threat modeling method for your project involves a careful consideration of several factors:
- Target Areas: Determine the focus areas such as risk, security, or privacy that are most critical to your project.
- Time Constraints: Consider the available timeframe for conducting thorough threat modeling.
- Experience Levels: Assess the experience your team possesses in performing threat modeling to choose a method that matches your capabilities.
- Stakeholder Involvement: Gauge the extent of involvement required or desired by stakeholders in the threat modeling process.
An overview of these methods and their key features is summarized in Table 3, designed to assist in making an informed choice. Moreover, these methods are adaptable to Agile workflows, capable of being integrated within the sprint cycles and repeated as necessary to align with continuous development and deployment environments.
In conclusion, the strategic application of threat modeling not only fortifies security measures but also ensures that these measures are continuously aligned with evolving project demands and emerging threats. This proactive approach is crucial for maintaining the integrity and resilience of your systems in an increasingly complex cybersecurity landscape.
Stay ahead in cybersecurity—reach out to us for expert advice or subscribe to our newsletter for the latest insights and updates delivered straight to your inbox.
- Threat Modeling: Designing for Security by Adam Shostack
- Cost of CyberSecurity
- Attack Tree
- Persona non Grata (PnG)
- OWASP Threat Modeling Cheat Sheet
- OWASP Application Security Verification Standard
- Threat Modeling Manifesto
Pingback: Elevate Cyber Defense: Start Threat Modeling Now - Manish Pandey