SO WHAT IS THREAT MODELING?
for uninitiated Think of threat modeling like a game where you’re trying to outsmart a villain who’s trying to break into a digital system. It’s a group activity where you draw out how the system works, sort of like a treasure map, and then you figure out all the ways the villain could sneak in or cause trouble. The aim is to find these weak spots before the bad guys do, so you can patch them up. It’s a bit of extra homework for the tech team and can slow things down, but it’s super important for keeping things safe. That’s why some smart tools are used to speed things up.
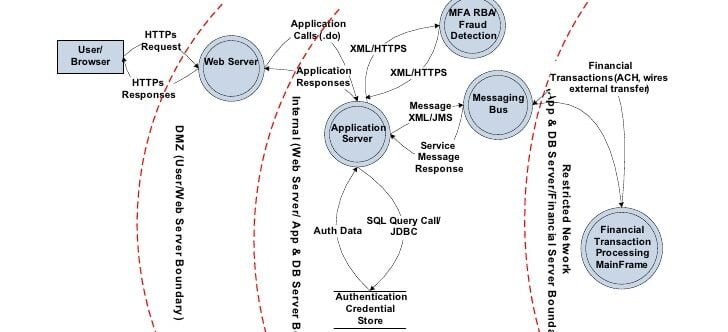
A rigorous process is integral to securing systems. This process involves a critical examination of your system’s architecture to anticipate and neutralize potential security threats, akin to chess where one predicts an opponent’s moves. We utilize sophisticated diagrams (4+1 or depending on the mercy of the development team) to map out your system’s landscape, identifying the attack surface and potential adversaries. While historically manual, this process could impose significant time constraints on your security and development teams, possibly hindering your software’s time-to-market. To circumvent these challenges, I recommend leveraging automated tools, which are indispensable in managing the complexity of contemporary software ecosystems and maintaining agility in your security practices.
“All Models are wrong but some models are useful“.
– George E.P Box
WHY TO EVEN THREAT MODELING?
Creating secure software is challenging due to the complexity of modern programs. Analogous to enhancing a building’s security system, recent guidelines emphasize thorough security reviews early in the development process. As developers, we’re now tasked with identifying and fixing security vulnerabilities as they arise, a crucial step for protecting against hackers. The industry is moving towards a Secure-by-Design approach, highlighted by OWASP’s latest guidance. This shift towards incorporating strict security measures, including threat modeling, from the start, is not just about compliance. It’s a strategic move to identify and mitigate risks early, making the development process more cost-effective and audits smoother, thereby strengthening an organization’s defense against cyber threats and enhancing its market position.
“Threat model is a fancy name for something we all do instictively.“.
– Adam Shostack
Strategic Approaches to Threat Modeling in SDLC
threat modeling is an indispensable part of the planning phase in the DevSecOps approach. It’s as crucial as any other business requirement, such as scalability or efficiency. Gartner emphasizes the integration of threat modeling within DevSecOps, treating it as essential as other design criteria like scalability or efficiency. Integrating threat modeling early on aligns security measures with your business objectives, enabling a more resilient architecture. This process demands close collaboration across your teams, Utilizing automation tools is key for efficiency and compliance, especially considering the complexity of current cybersecurity regulations. It’s about building a security-first culture, where every design decision upholds the integrity of your software throughout its lifecycle.
“Threat Modeling is Evil Brainstorming”.
– Tanya Janca
Strategies and Techniques
universal approach to threat modeling doesn’t suit the diverse security needs of different organizations. Each organization must choose a threat modeling methodology that aligns with its specific characteristics and security requirements. A custom-fit approach is crucial for making threat modeling both practical and effective across various organizational contexts.
Asset-Centric Approach: Focuses on critical assets, prioritizing their confidentiality, integrity, and availability using tools like asset inventories and risk ranking.
Attack-Centric Approach: Views from the attacker’s perspective, identifying potential attack vectors and entry points, and using techniques like threat actor profiles and attack simulations.
System-Centric (Software-Centric) Approach: Analyzes individual system components and interfaces, identifying vulnerabilities with tools like design specifications and vulnerability assessments.
Risk-Centric Approach: Evaluates overall system risk, incorporating risk analysis techniques and tools like risk matrices and business impact analysis.
Here Layered Threat Modeling An Architectural Approach suggested by Michael Boeynaems is also a good prospective to go through.
“Very few organizations will have the time or resources to threat model their entire ecosystem. Assuming you do not have that luxury, you still can realize quite a bit of value just by adopting the mindset of looking for blind spots and questioning assumptions”.
– ED Moyle
Frameworks for Threat Modeling
STRIDE: Focuses on categorizing threats into six types. It’s effective early in development, helping teams proactively address security.
PASTA: A business-driven, risk-centric method. It follows seven structured steps, emphasizing on simulating and testing threats against business objectives.
TRIKE: Combines asset-centric and attack-centric analysis. It involves understanding attacker goals and mapping potential attack paths.
OCTAVE: Tailored for both large and small organizations, this risk-based approach aligns with business objectives and includes scenario-based assessments.
FOUR QUESTION FRAMEWORK
Adam Shostack discusses this in detail in Threat Modeling: Designing for Security
“What are we building?”: This involves producing architectural or design documents, data flow diagrams, asset inventories, and data classifications.
“What can go wrong?”: Identifying main security and privacy threats to system components or assets, typically using a threat list like STRIDE or OWASP Top 10.
“What are we going to do about it?”: Implementing security controls or defense-in-depth mechanisms to mitigate these threats.
“Did we do a good enough job?”: Conducting a retrospective analysis to learn from the process and continuously improve the effectiveness of threat mitigations.
Defining Processes and Expectations
- Review Timing & Frequency: Align review schedules with development cycles and project timelines, adapting to either post-sprint planning or regular intervals as fits the workflow.
- Roles & Participation: Define clear roles for a cross-functional team engagement, ensuring a collaborative approach across security and software disciplines.
- Communication: Establish designated channels for all threat modeling communications, including planning, logging, and alerts, to maintain stakeholder synchrony.
- Review Scope: Ensure reviews comprehensively assess system vulnerabilities, covering all potential security risks.
- Risk Management: Implement a framework for risk categorization and prioritization based on impact, guiding mitigation strategies.
- Threat Intelligence: Stay informed on emerging threats to gauge potential organizational impact.
- Security Controls: Identify and plan for the implementation of remedial and mitigative actions against identified threats.
- Preparation Guidelines: Set clear preparation expectations for stakeholders to enhance meeting efficiency.
- SLAs: Define SLAs for threat response to guarantee timely mitigation efforts.
- Artifacts: Specify required artifacts for review preparation, ensuring readiness and comprehensive risk assessment.
Creating Threat Modeling Artifacts
- Asset Inventories and Trust Boundaries: A comprehensive inventory of assets, components, and trust boundaries is the foundation of effective threat modeling. This involves identifying all elements involved in the system, including sensitive data and valuable resources that might be targeted by attackers.
- Data Flow Diagrams (DFDs): DFDs are visual tools that help in understanding how data moves through the system. The use of specialized threat modeling tools can greatly enhance the effectiveness of these diagrams by identifying potential vulnerabilities and attack vectors.
- Design Diagrams: In complex systems, additional diagrams like UML sequence diagrams can be invaluable in understanding intricate sequences and interactions, particularly around authentication and authorization protocols.
- Security Requirements Documentation: Documenting security requirements, use cases, and abuse cases ensures that the threat modeling process remains focused on addressing specific security concerns inherent to the system under review.
Leveraging Automation Tools
- Efficiency and Accuracy: Automation tools in threat modeling provide significant time-saving benefits. They facilitate the import of system components from resource files, such as Terraform configurations, eliminating manual entry and enabling quick generation of diagrams.
- Comprehensive Analysis: These tools can identify shared components, libraries, and patterns, thus reducing effort and highlighting risks that affect multiple areas of the system.
- Establishing Trust Boundaries: By identifying interfaces and interactions, automation tools enhance the accuracy and consistency of the artifacts created.
Measuring Success
- Importance of Measuring Success:
Threat modeling is an investment in time and resources. Therefore, it’s crucial to ensure it yields valuable results and contributes to process improvement.
- Utilization of Key Performance Indicators (KPIs):
KPIs are essential metrics that help assess the effectiveness of the threat modeling process. These include:
- The number of identified threats, which indicates the effectiveness of the threat detection process.
- The closure rate of high-risk threats, crucial for understanding the efficiency of the response to critical vulnerabilities.
- The reduction in security incidents, reflecting the overall impact of threat modeling on enhancing security posture.
- The number of security controls implemented as a result of threat modeling, showing the direct contribution of the process to security enhancement.
- Operating costs, providing insight into the financial efficiency of the threat modeling process.
- Role of Automation Tools:
Automation tools are pivotal in collecting and analyzing KPIs, ensuring a comprehensive assessment.
- They facilitate the generation of reports and visualizations, making it easier to track and understand performance against set KPIs.
- These tools also assess the adequacy of mitigation strategies and measure time and resource savings, highlighting efficiency gains.
- Coverage and completeness metrics offered by these tools ensure the thoroughness of the threat modeling process.
- Compliance reports generated automatically demonstrate adherence to regulatory requirements and best practices.
- Continuous Improvement and Real-Time Insights:
Live dashboards provided by automation tools offer real-time insights into the current threat status, mitigation progress, and overall security posture.
Monitoring these metrics over time is essential for tracking improvement and success in the overall threat management strategy.
In summary, a structured approach to measuring the success of threat modeling, backed by KPIs and supported by automation tools, is critical in ensuring that this process is not only effective but also contributes to the continuous improvement of the organization’s security practices.
Utilization of outcome in other domains
Security Testing
- Engineer precision-targeted security validations leveraging threat modeling intel.
- Stratify Penetration testing protocols to concentrate on segments with elevated risk profiles.
- Embed automated mechanisms to escalate testing proficiency and expansiveness.
Supply Chain Oversight
- Conduct rigorous risk assessments within the supply chain, guided by threat modeling insights.
- Scrutinize and govern vendor security practices, aligning with identified threat paradigms.
- Craft incident response blueprints to navigate supply chain vulnerabilities effectively.
Incident Management
- Harness threat modeling insights for strategic incident response preparedness.
- Facilitate swift incident detection and analysis, anchored in threat intelligence.
- Cycle incident learning back into threat modeling to continuously refine response acumen.
Risk Governance
- Allocate risk management resources with a focus on probability and impact, as illuminated by threat modeling.
- Formulate and implement security policies and protocols that directly address discerned risks.
- Fortify compliance and auditing efficacy, underpinned by an intricate understanding of the threat landscape.
We’d love to hear your thoughts and questions about threat modeling! Please feel free to reach out and share your insights with us through our contact form. Your feedback and queries not only help us improve, but also contribute to a broader understanding and knowledge-sharing within our community.
Stay ahead in cybersecurity—reach out to us for expert advice or subscribe to our newsletter for the latest insights and updates delivered straight to your inbox.
- Threat Modeling: Designing for Security by Adam Shostack
- OWASP Threat Modeling Cheat Sheet
- OWASP Application Security Verification Standard
- Threat Modeling Manifesto