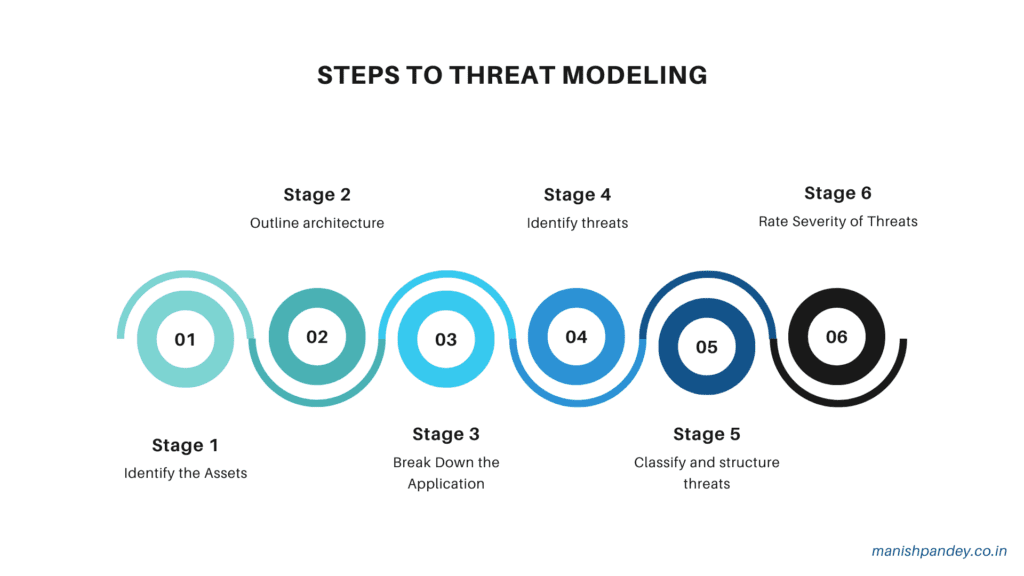
Cyber Resilience: How to Implement Cutting-Edge Threat Modeling Techniques
In today’s rapidly evolving technological landscape, virtually all software ecosystems are susceptible to a myriad of security threats. These threats are escalating in sophistication and scale, evidenced by a 151% surge in malware exploiting software vulnerabilities in Q2 2018 alone. Furthermore, it’s projected that by 2021, the financial repercussions of cyber-crime will skyrocket to an […]
Cyber Resilience: How to Implement Cutting-Edge Threat Modeling Techniques Read More »