Transform Your Security Strategy with Leading Threat Modeling Tools
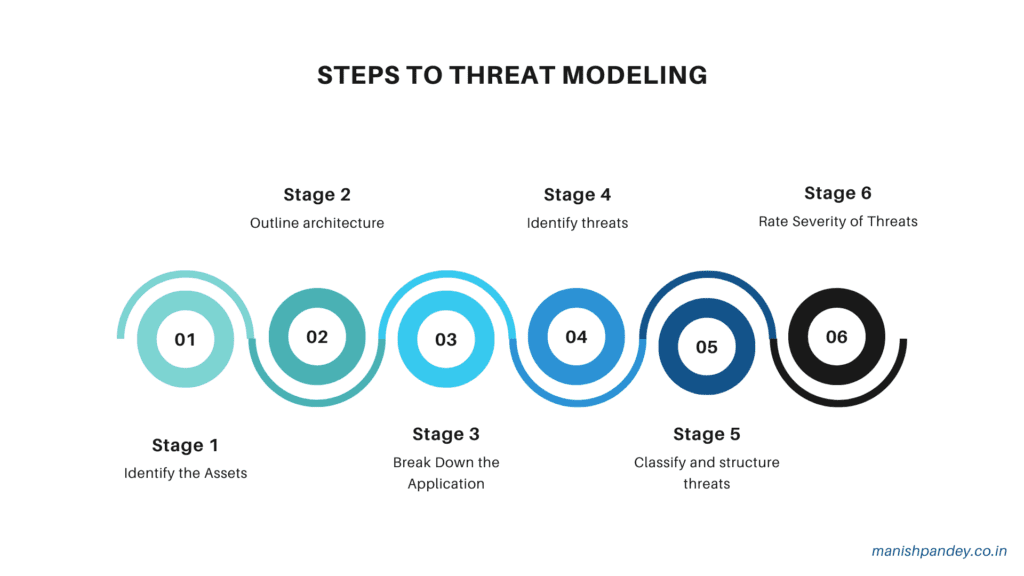
1. Overview of Threat Modeling Historical Context Threat modeling, as a discipline, has its roots in the early days of computer security. Initially, security efforts were largely reactive, focusing on responding to incidents after they occurred. However, as information systems became more complex and interconnected, the need for a proactive approach to security became evident. […]
Transform Your Security Strategy with Leading Threat Modeling Tools Read More »