As Ai’s adoption accelerates in enterprises —integrating AI agents, LLMs, cloud SaaS, automation, and data pipelines into every business function—the threat landscape is evolving faster than ever. Security architects and CISOs now face a unique challenge: defending complex, layered systems where threats can cascade and business impact is more severe than in “classic IT.”
This guide delivers a practical, layered blueprint to assess and mitigate risk for all modern digital architectures—not just those built around agentic AI.
1. Why Layered Security Is Essential in Modern Enterprises
AI-powered systems, cloud platforms, microservices, and RAG pipelines introduce new pathways for compromise. A single vulnerability in one layer (models, data processing, cloud infra, APIs, or integration points) can cascade and threaten revenue, compliance, or reputation.
Solution: Map, defend, and continuously monitor every logical and operational layer. CSA MAESTRO Framework
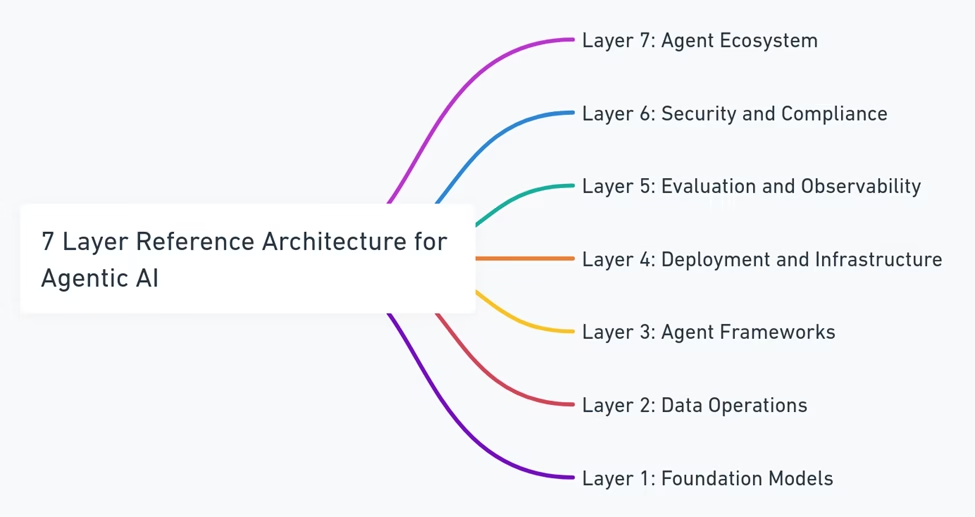
2. Layer-by-Layer Threats & Mitigations
a. Models & Machine Learning Layer
- Threats: Adversarial attacks, data poisoning, model leakage/theft, bias exploitation, output manipulation.
- Controls:
- Adversarial “red teaming” and robust testing.
- Provenance tracking of training data and third-party models.
- API rate-limiting, explainability, and policy-driven access.
b. Data Operations & Pipelines
- Threats: Data corruption, exfiltration, injection, malicious pipeline manipulation.
- Controls:
- Encryption and access control.
- Monitoring for anomalous flows and tampering.
- Input validation at all ingestion/processing points.
c. Application Frameworks & Integration
- Threats: Supply chain compromise, dependency injection, code/module poisoning, API flaws.
- Controls:
- Secure SDLC, SBOMs, and regular vendor/library audits. OpenSSF MLSecOps Whitepaper
- API gateway hardening.
- Automated dependency scanning. OWASP ML Security Top 10
d. Deployment & Infrastructure (Cloud and On-Prem)
- Threats: Orchestration layer attacks, container/image tampering, resource hijacking, lateral movement, misconfigurations.
- Controls:
- Zero trust segmentation.
- Continuous infrastructure-as-code (IaC) validation.
- Cloud posture management, runtime monitoring. CloudGuard.ai MLSecOps Guide
e. Observability, Evaluation, and Monitoring
- Threats: Log/telemetry manipulation, blind spots, monitoring DoS, sensitive data leaks.
- Controls:
- Isolated, tamper-evident logging.
- Threat-hunting and anomaly detection.
- Risk-based alerting and incident cross-correlation.
f. Security, Privacy & Compliance (Across Layers)
- Threats: Gaps in consent, DLP failures, bias or fairness regulatory penalties, auditability shortfalls.
- Controls:
- Automated compliance tracking (GDPR, DPDP, SOX, sectoral).
- Privacy-by-design in all data touchpoints.
- Periodic compliance drills and impact assessments.
g. Business Ecosystem and Third-Party Risk
- Threats: Supplier compromise, SaaS/partner risk, data sharing missteps, external registry or marketplace manipulation.
- Controls:
- Due diligence, continuous vendor risk monitoring.
- SLA-backed controls in contracts.
- Business continuity and recovery playbooks validated against outside-in scenarios.
3. Systemic & Cross-Layer Risks
- Supply Chain & Dependency Risks:
A single library or SaaS service compromise can disrupt multiple business units. - Cascading Failure Scenarios:
Normal errors become existential risk when propagated across models, pipelines, and customer touchpoints. - Incident Response Blind Spots:
Gaps in monitoring or siloed data flow can hinder rapid mitigation.
Controls:
Establish end-to-end observability, formalize incident exercises that cross team and system boundaries, and empower leaders to “pull the trigger” on business-side recovery—fast.
4. DDoS, API Abuse, and Legacy Threats—Reimagined
- Modern DDoS: APIs and ML endpoints are primary targets; adaptive scale/defense strategies, and surge preparedness are required.
- Credential and Device Hygiene:
Passkey rollouts and kill-switch playbooks for compromised identities/devices are now board-level issues.
5. Zero Trust: More Than a Network Perimeter
- Principle:
Apply least privilege, adaptive verification, and continual trust assessment to every system, application, user, device, and service. - How:
Map trust relationships, continuously scan for privilege drift, and automate threat-driven context switches (e.g., trigger re-auth or containment on telemetry anomalies).
6. Privacy, Consent, and Data Governance—Boardroom Imperatives
Data is gold—and toxic if mishandled.
- Track every use, movement, and consent status.
- Prepare for regulatory audits with deep, live data flow diagrams and breach simulation data.
7. From “Best Practice” to Results: Leadership Actions
- Security Architects:
Own the threat models. Regularly simulate adversary scenarios; treat business flow mapping as a core activity, not a supplementary task. - CISOs:
Elevate security and privacy to CEO/board dashboards. Quantify business risk and resilience, not just patch coverage. Build cross-functional, cross-silo readiness.
Immediate Next Steps for Leadership:
- Conduct a layered risk review of core business systems—map threats, controls, and monitoring gaps across all layers.
- Audit key third-party and model dependencies.
- Sponsor a cross-functional incident drill involving model attack, data breach, and supply chain failure in a single scenario.
- Publish a one-page, layered security dashboard for board review—focus on risk, readiness, and recent learnings.
8. Summary and Vision
Secure modern digital business isn’t built on static controls—it requires layered, adaptive strategies that bridge architecture and executive vision. By mapping, defending, and governing every layer, organizations unlock resilience, trust, and opportunity in the age of AI-empowered enterprise.
Stay tuned for in-depth briefings and board-ready playbooks tailored to evolving threats—because in security, readiness and leadership are inseparable.